























About us
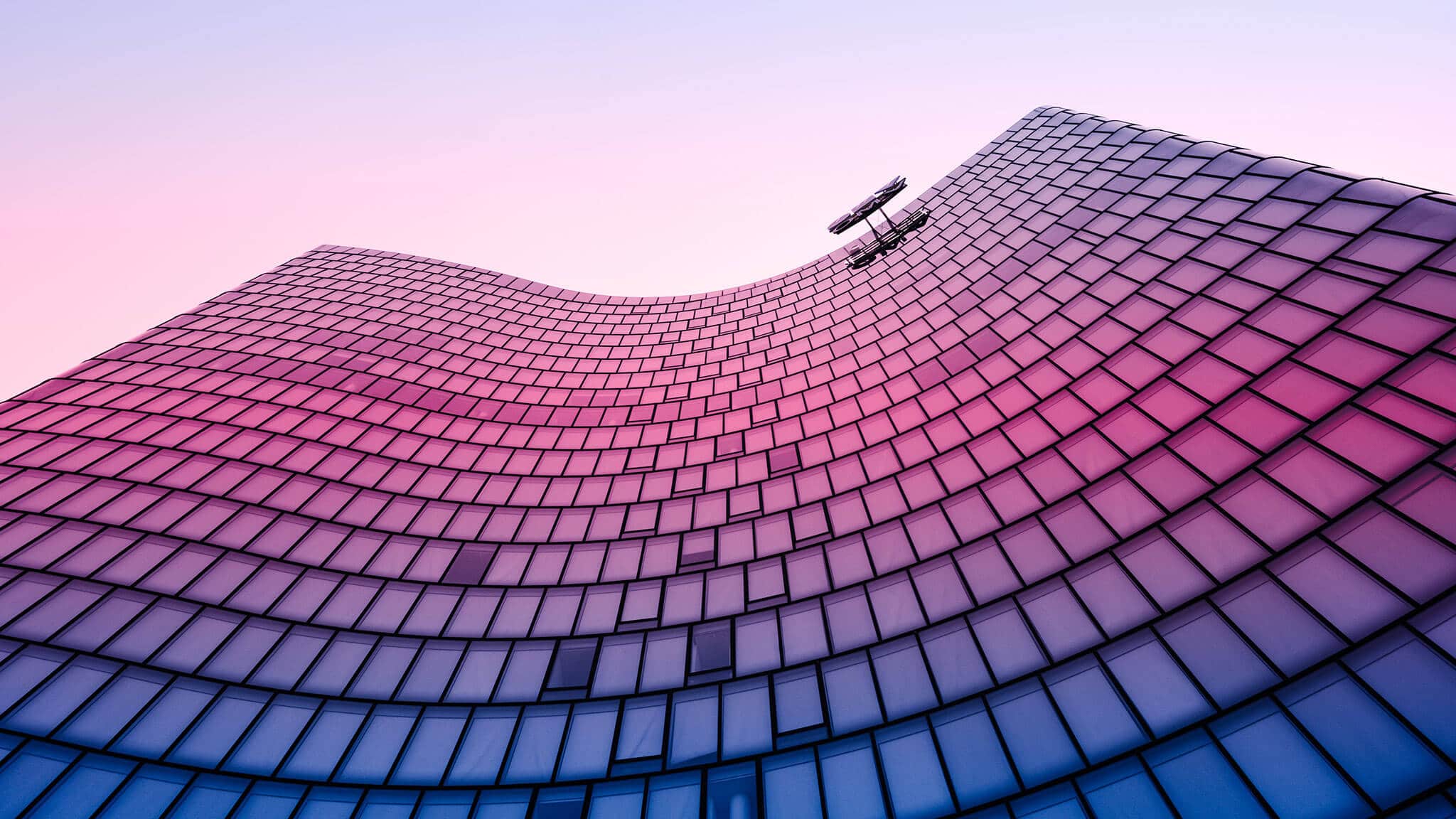
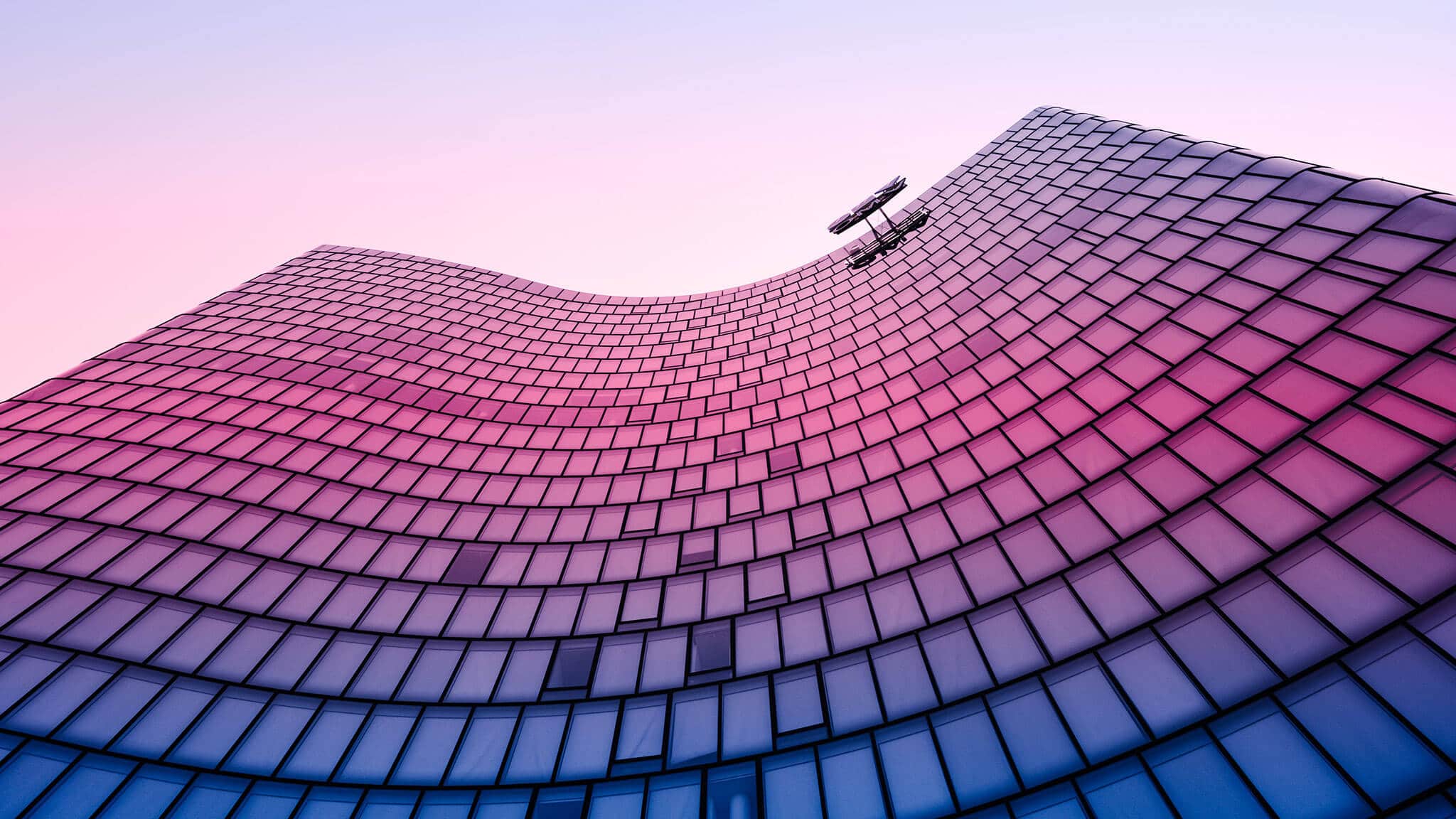
Make waves with us
By combining the power of Microsoft cloud technology with world-class identity, cyber security, managed services and a team of talented people, we take our clients on a journey of secure cloud transformation.
If you want to realise your organisation’s full potential, partner with us.
WHAT WE DO
Greatness is small things done well
We focus on getting the fundamentals done right to keep you moving forward. Click on the plus icons below to discover what we do.
-
Give the right people the right access.
-
Work safely, wherever you are in the world.
-
Modernise your business with cloud technology.
-
Empower your business with advanced security solutions.

OUR APPROACH
Our fail safe approach to greatness
Ready to lead the way? Here’s how we shape your path to transformation.
Identify and envision
First up. We identify all gaps and challenges inside your organisation – and decide what future you’re building.
Discover and design
We really get to know you. Then we design a solution to solve your challenges and help power your potential.
Build and deploy
Time to get real. We build and deploy your new solution. Confident that you’ll start getting great outcomes.
Support and manage
No room for risk. We keep costs to a minimum and make sure your solution runs smoothly and efficiently.
The thing that stands out about Kocho is their level of professionalism and the experience they have in the identity and access management space. They are market leaders and that really shows.
Stuart Purkiss-Webb
Infrastructure Architect, Aviva
NEED HELP BECOMING GREATER?

AWARDS & ACCREDITATIONS
Striving for greatness.
We’ve been a leading Microsoft Partner for over 20 years.
Our ability to achieve real business value for our clients has been recognised by Microsoft. It’s why we’ve won multiple Partner of the Year awards and Gold Competencies.



Featured
Who we've helped

Transforming a leading medical imaging service provider with Microsoft Cloud


Don't Miss
Great content and resources

What is Microsoft Entra?
What is FinOps and how is it transforming cloud computing?

Kocho raise £1,500 for St David's Hospice with 3 Peaks walk in Wales

Microsoft Tech Update: Security Special
Gain up-to-date knowledge on the features and functionality of Microsoft’s key cloud, identity and security technologies.
Got a question? Need more information?
Our expert team is here to help.

